In the ever-evolving world of governance, risk management, and compliance (GRC), adaptation is key. We at NorthGRC (formerly Neupart) have recognized the need to evolve and expand our horizons to better serve you, our valued partners. Today, we're thrilled to introduce our new name NorthGRC. A name that reflects our growth, innovation, and commitment to providing best-in-class GRC solutions.
Neupart transforms into NorthGRC
[fa icon="calendar'] Monday, 04 December 2023 / by NorthGRC under GRC, NorthGRC
How will NIS2 impact an information security manager?
[fa icon="calendar'] Wednesday, 05 July 2023 / by Neupart under ISO 27001, NIS2, CISO, ISO 27002
NIS2 will have practical significance for you as an information security manager, as the requirements of the directive are directly aimed at the administration of information security.
If you need further information about NIS2, click here to get a handle on the NIS2-basics.
GDPR Compliance: Bridge the Gap
[fa icon="calendar'] Wednesday, 08 March 2023 / by Jakob Holm Hansen under compliance, GDPR
Even though GDPR is right around the corner, it makes a lot of sense - practically and financially - to maintain your traditional information security measures, because compliance with the Data Protection Regulation both can and should build upon your existing security measures.
Choosing the right business continuity scenarios for your BCP
[fa icon="calendar'] Wednesday, 08 June 2022 / by Jakob Holm Hansen under business continuity strategy, Business Continuity Planning, Information Security Management, business continuity scenario, ISMS, BCP, disaster recovery
Our most recent blog post dealt with The three golden rules of a business continuity plan. This time, we continue in the world of business continuity planning and take a closer look at scenarios and strategies.
The three golden rules of a business continuity plan
[fa icon="calendar'] Monday, 30 May 2022 / by Jakob Holm Hansen under Business Continuity Planning, Information Security Management, IT risk assessment, information security policies, SecureAware BCP, ISMS, BCP
"How long should a business continuity plan be?" This is a question we often hear from our customers. My answer usually is: "As short as possible!" The truth is that the perfect business continuity plan (if such a thing exists) should be three - sometimes contradictory - things at once:
How to Handle a GDPR Breach
[fa icon="calendar'] Sunday, 08 May 2022 / by Jakob Holm Hansen under GDPR
a personal data security breach
Our new white paper, GDPR - Handling Personal Data Security Breaches in Three Phases, considers the formal requirements for handling a personal data security breach in accordance with GDPR and sets out guidelines for the preparation and anchoring of appropriate contingency measures.
Do you need to explain what ISO 27001 is?
[fa icon="calendar'] Tuesday, 06 April 2021 / by Neupart under ISO 27001, Information Security Management, Information risk management, ISMS
We've produced this video to help you communicate the main components of an Information Security Management System (ISMS), as described in ISO 27001. You may need this information when talking to your company's management team, and getting onboard in securing your business.
Watch the video explaining what ISMS and ISO27001 are.
These four facts about ISO 27001 and an ISMS are vital in your work as someone who deals with information security, risks, or IT in general. Understanding the fundamentals and getting started the right way is the biggest step of them all.
The four facts about ISO27001 are:
- ISO27001 is an international standard about how to manage your information security
- You must know your risks!
- You need an Information Security Policy
- It is a process, not a project!
We are experts in information security (ISO 27001/-2) and GDPR, and our ISMS is an intuitive cloud-based platform where you can handle everything you need in regards to both ISO27001/-2 and GDPR.
Get deeper into information security, GDPR, and our ISMS either by browsing our knowledge base or visiting the main ISMS page here.
Risk assessments must align with business goals
[fa icon="calendar'] Monday, 16 December 2019 / by Jakob Holm Hansen under information security, Risk assessments, risk treatment
It is not just a huge help for general management when company risk assessments are based on concrete business goals. Business-based risk assessments also help information security managers to prioritize what scarce resources they have.
Here's how to get management support for information security initiatives
[fa icon="calendar'] Friday, 28 June 2019 / by Jakob Holm Hansen under information security, annual plan, compliance programme, management support
It is gradually becoming more and more necessary to actively secure management support for any new business initiatives – not least when it comes to information security. The support of decision makers is absolutely essential for the successful operation and development of a compliance programme. But how can we go about getting this support? Our CEO cuts through the rhetoric and offers up five pieces of advice to those responsible for information security.
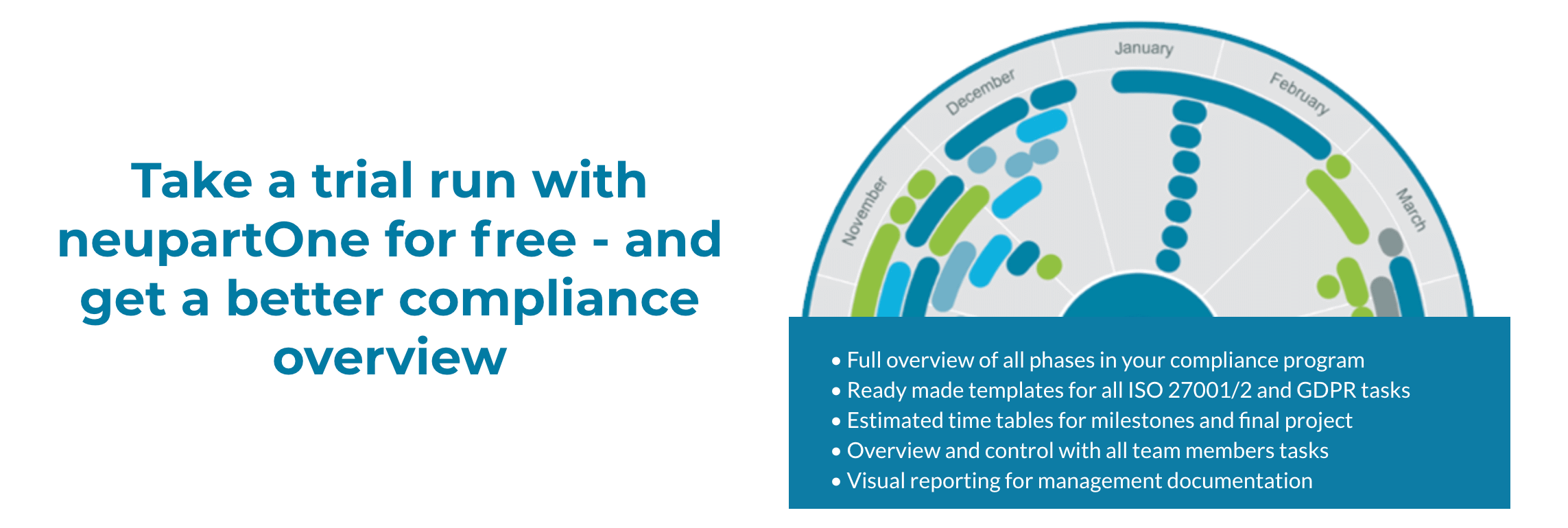
A compliance planning tool gives information security managers an automatic plan
[fa icon="calendar'] Wednesday, 01 May 2019 / by Jakob Holm Hansen under Information Security Management, annual plan, compliance programme
There used to be many unknown factors for information security managers to take into account when implementing and maintaining a security standard. That is no longer the case. A compliance planning tool creates a well-arranged plan for the compliance work and automatically combines all the tasks in a single annual plan.